- Support Home
- Knowledge Base
- Account Management
- Account Security
- Setting Up Single Sign-On (SSO) in Taguchi
Setting Up Single Sign-On (SSO) in Taguchi
Introduction
Taguchi supports Single Sign-On (SSO), allowing users to authenticate using external identity providers like Azure Active Directory (Azure AD). This simplifies the login process, centralizes user authentication, and enhances security by reducing the need for multiple login credentials. By integrating SSO, organizations can streamline access management and provide a seamless login experience for their users.
What Does Taguchi Support in Terms of SSO?
Taguchi integrates with Azure AD for SSO and supports the following configurations:
- Separate Azure AD Tenancy: Taguchi can authenticate users from a different Azure AD tenancy.
- Same Azure AD Tenancy, Specific Domain: Taguchi can authenticate users from a specific domain within an existing Azure AD tenancy.
Once an identity provider is linked, only user accounts authenticated through that identity provider will be accessible. Existing user accounts in Taguchi will remain unaffected unless explicitly linked to an identity provider.
SSO Setup Instructions
You will need to be an administrator of your organisation in order to set up SSO in Taguchi
Option 1: Setting Up with a Separate Azure AD Tenancy
To authenticate users from a different Azure AD tenancy, an admin must:
- Log in to Taguchi.
Navigate to Settings > Users.
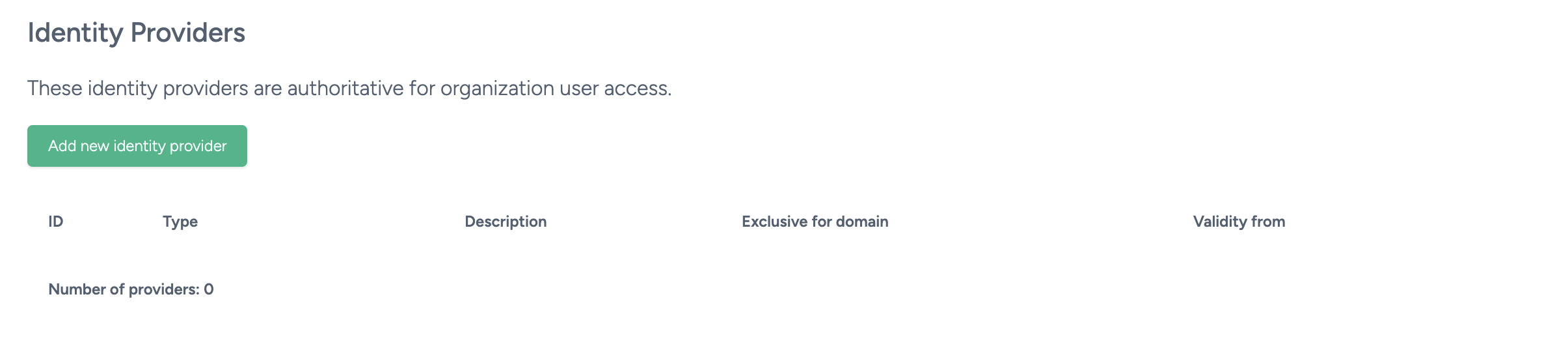
Scroll down and click Add new identity provider.
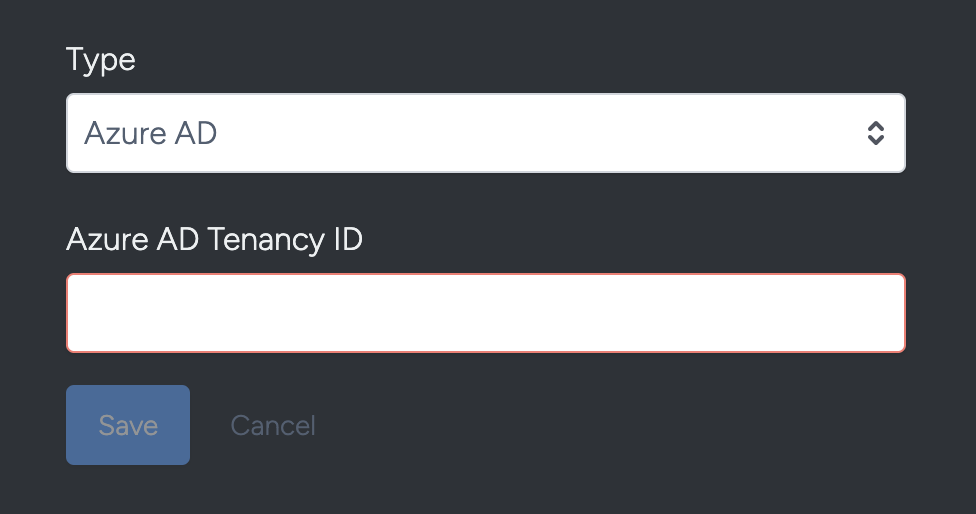
Enter the Azure AD Tenancy ID and click Save.
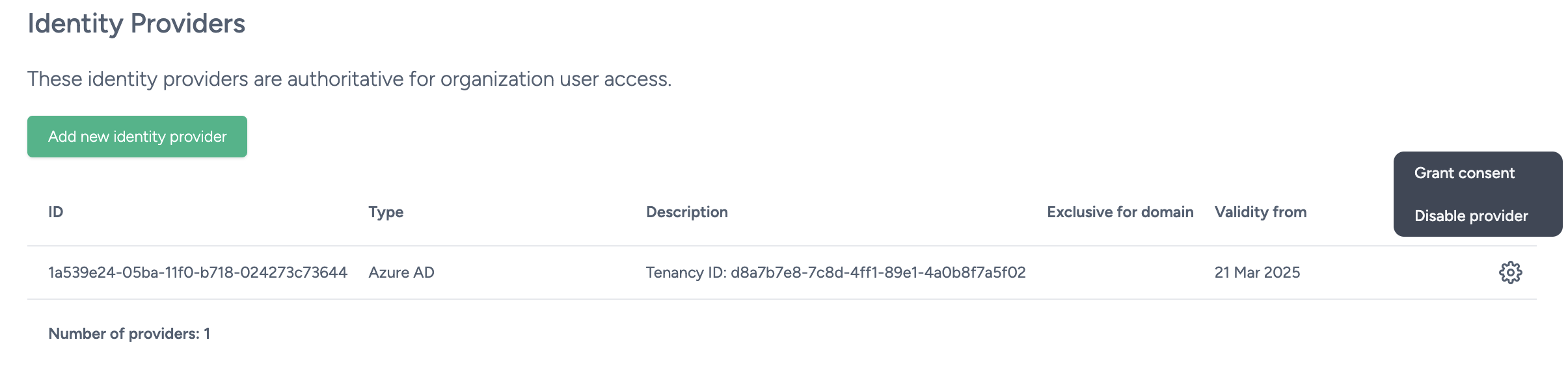
- In the Identity Providers table, click the gear icon next to the tenancy entry.
- Select Grant consent to authorize Taguchi as an app in that tenancy.
Option 2: Using the Same Azure AD Tenancy but Allowing a Specific Domain
To authenticate users from a specific domain within the same Azure AD tenancy, the admin should:
Under Settings > Users, Create a new user account in Taguchi using your company domain email
Once the new account is created, please reach out to Taguchi Support so that we can make the existing tenancy authoritative for the new domain. This will ensure all users with email addresses matching that domain are seamlessly redirected to the sign-in page for that tenancy.
If this option is not configured, the relevant user accounts will still be linked to your tenancy. However, users will be required to log in via the O365 My Apps portal the first time they access Taguchi.
Making the Tenancy Authoritative for a Domain
If you wish to streamline the login experience, Taguchi can optionally make the tenancy "authoritative" for a domain. This feature ensures that all users attempting to log in with an email address matching that domain are automatically redirected to the sign-in page for that tenancy. As a result, even new users in your domain will have a seamless login experience without any interruptions.
To enable this feature, please reach out to Taguchi Support. Our team will assist you in setting the tenancy as authoritative for your domain to provide a smooth and uninterrupted login experience.
Troubleshooting
- Ensure the Azure AD Tenancy ID is entered correctly when setting up the identity provider.
- Verify that the admin account has the appropriate permissions in Azure AD.
- Confirm that consent has been granted for Taguchi in the Identity Providers table.
For further assistance or to enable the authoritative domain feature, please contact Taguchi Support.
